March 10, 2025
The Importance of OT Security
Why OT Security Matters Now
Cyber threats targeting operational technology have escalated quickly.
Ransomware groups, nation-state actors, and opportunistic attackers now view industrial operations as high-value targets because disruption creates immediate operational and financial pressure.
Industrial environments have also changed. Remote access, centralized monitoring, cloud-based analytics, and tighter IT/OT integration are now common.
These capabilities improve visibility and efficiency, but they also introduce new exposure points that many facilities were never designed to handle.
Most industrial control systems were built with reliability and uptime as the top priorities. Security was often assumed rather than engineered. As connectivity increases, those assumptions no longer hold.
This shift highlights why OT security is important now. Risks have evolved faster than the protections surrounding critical operations.
Key Risks to OT Environments
OT environments face a mix of technical limitations and operational realities that increase exposure.
Common risks
- Outdated control systems, such as PLCs, DCS platforms, and SCADA environments
- Limited or nonexistent segmentation between IT and OT networks
- Unpatched operating systems, firmware, and applications
- Remote access connections without strong authentication or monitoring
- Insider threats, both malicious and unintentional
- Weak backup, recovery, and disaster response processes
- Legacy communication protocols without encryption or authentication
- Human error due to limited cybersecurity awareness
These vulnerabilities often accumulate gradually. Individually, they may seem manageable. Together, they create multiple entry points and increase the likelihood that a single incident escalates into a significant disruption.
Potential Consequences of Security Breaches
When OT security fails, the consequences extend beyond data loss. These systems control physical processes, so the impact is immediate and costly.
Production Stoppage
A cyber incident can halt production by disabling controllers, corrupting logic, or forcing precautionary shutdowns. Even short interruptions can lead to missed targets, wasted materials, and downstream supply chain disruption.
Safety Hazards
OT systems regulate pressure, temperature, speed, and chemical reactions. Altered logic or manipulated sensor data can reduce situational awareness, leading operators to act on inaccurate information.
This loss of control can result in unsafe conditions, equipment damage, environmental releases, or injuries. Cyber-related safety incidents undermine trust in both systems and procedures.
Data Loss
Operational data, configuration files, and backups are essential for stable operations. A breach can erase or corrupt this information, slowing troubleshooting and recovery.
Recreating lost data often requires manual effort, reverse engineering, or vendor involvement, which increases downtime and costs.
Intellectual Property
Industrial environments contain valuable intellectual property, including control strategies, automation logic, proprietary recipes, and production methods.
Once accessed, this information can be copied or reused indefinitely. Unlike equipment, intellectual property can’t be repaired once exposed.
Regulatory Fines
Many industries operate under strict safety, environmental, and cybersecurity regulations. A breach involving control systems may trigger investigations, disclosures, and financial penalties.
Reputational Damage
Customers and stakeholders expect reliability. A public OT security incident can damage credibility and raise concerns about operational maturity.
Rebuilding trust often takes longer than restoring systems.
Costly Recovery
Recovery rarely ends with system restoration. Costs often include forensic analysis, hardware replacement, redesigns, legal support, and extended downtime.
In many cases, recovery costs exceed the investment required for preventive measures.
What Good OT Security Looks Like — Core Principles
Effective OT security relies on layered controls that reduce risk without upsetting operations.
Network Segmentation
Clear boundaries between IT systems, OT environments, and critical control zones limit lateral movement. Segmentation also simplifies monitoring and incident response.
Secure Remote Access
Remote access remains necessary for maintenance and vendor support. Without controls, it becomes a common attack vector.
Secure access relies on VPNs, multi-factor authentication, role-based permissions, and monitoring. Access should be limited in scope and duration with accountability for every connection.
Patching and Updates
Patching OT systems presents challenges, but ignoring updates increases exposure. A structured approach balances operational constraints with risk reduction.
This may include scheduled maintenance windows, staged testing, and compensating controls for systems that can’t be patched immediately.
Asset Inventory
An accurate asset inventory is foundational. Organizations must know what devices exist, where they reside, and how they communicate. Without this visibility, risk assessment and response are difficult.
Incident Response Planning
OT incidents differ from IT events. Safety, uptime, and physical processes require equal consideration.
An OT-specific response plan defines roles, communication paths, and decision authority. Regular exercises improve response speed and confidence.
Regular Audits
Audits identify gaps before incidents occur. Reviews should cover technical controls and operational practices, including access management and change control.
Employee Training
Operators, engineers, and managers interact with OT systems daily. Training helps teams recognize suspicious activity and follow secure procedures.
Intrusion Detection
OT-specific detection tools monitor traffic and behavior without interfering with operations. Early visibility supports faster investigation.
Backups and Redundancy
Reliable backups and redundant systems support recovery. Backups should be protected, tested, and stored securely. Redundancy helps critical processes continue during failures or attacks.
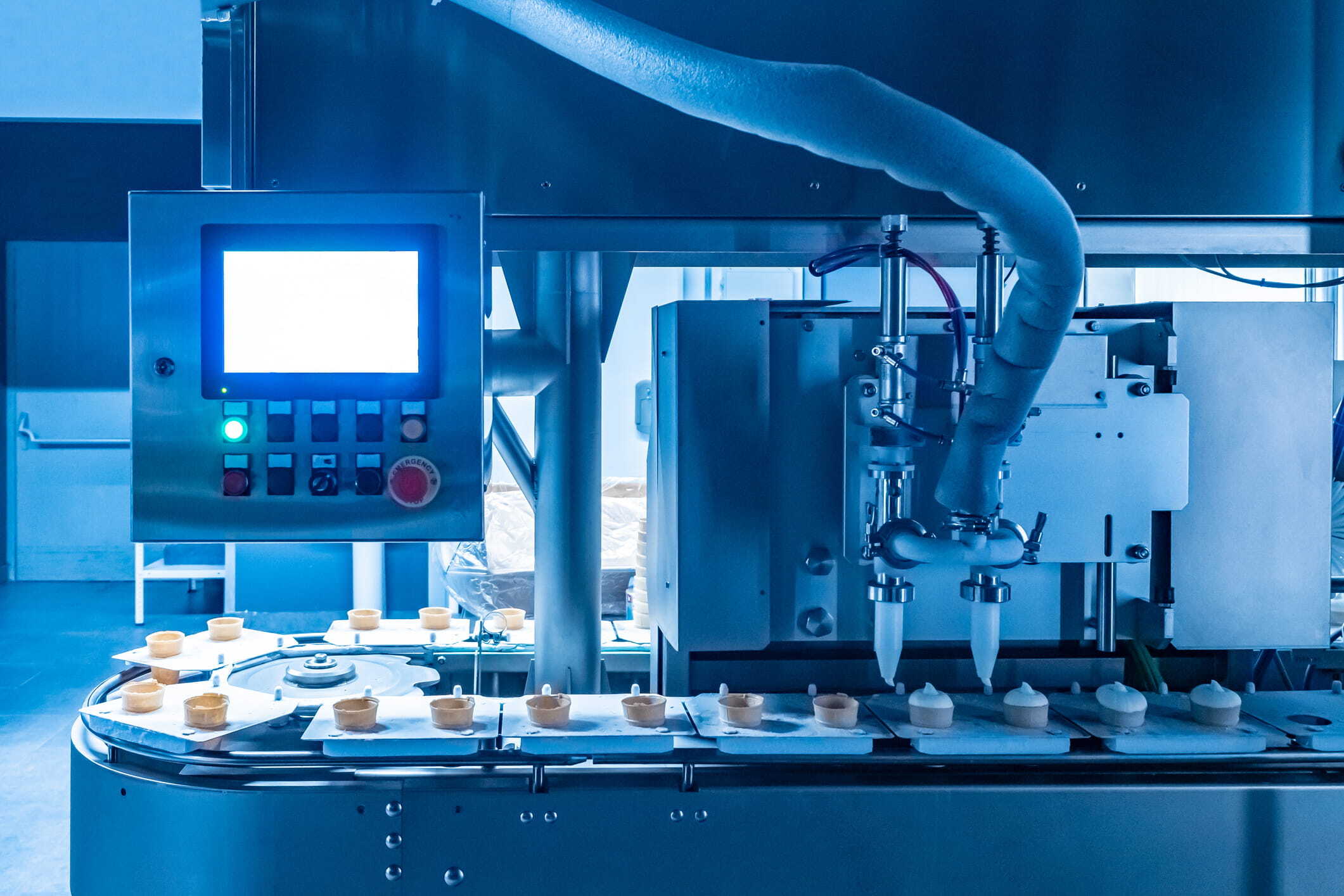
Integration of OT Security With Automation and Controls
OT security is most effective when embedded into automation and control system design. Treating security as an afterthought often leads to fragile controls and workarounds.
Secure architectures account for network layout, access control, protocol selection, and monitoring from early design stages. Fail-safe behavior ensures systems move to safe states if communication or control is lost.
Layered safeguards increase resilience. When paired with OT network automation, organizations can scale operations while maintaining consistent security and visibility.
Benefits of Investing in OT Security
OT security provides value beyond risk reduction.
- Reduced risk of downtime and catastrophic failure
- Better audit readiness and documentation
- Protection of physical assets and intellectual property
- More predictable, stable operations
- Lower recovery and legal costs compared to breach response
How The EOSYS Group Supports OT Security for Clients
EOSYS provides hands-on OT security services for industrial environments. Work includes vulnerability assessments, control system architecture reviews, and network segmentation planning that accounts for operational constraints.
Legacy systems can be upgraded or retrofitted, and teams receive training to recognize threats and maintain secure practices. Ongoing monitoring helps systems remain stable as operations and technology evolve.
Actionable Steps for Industrial Operators — A Security Checklist
Use this checklist to evaluate your current OT security posture.
- Inventory all OT assets
- Map IT and OT networks and connection points
- Review access permissions and authentication
- Evaluate patching and update practices
- Verify backups and test restoration procedures
- Confirm cybersecurity training coverage
- Secure all remote access paths
- Develop and test an OT-focused incident response plan
Securing Operations for the Future
OT security protects safety and productivity while supporting long-term operational success. As industrial environments become more connected, proactive security measures aren’t optional anymore.
Working with experienced OT system integrators helps ensure security measures match real-world operational demands. EOSYS helps organizations looking to assess risk and strengthen industrial security programs.